- cross-posted to:
- secops@lemmy.world
- cross-posted to:
- secops@lemmy.world
Ever hear one of those stories where as it unravels, you lean in ever closer and mutter “No way! No way! NO WAY!” This one, as far as infosec stories go, had me leaning and muttering like never before. Here goes: Last week, someone reached out to me with what
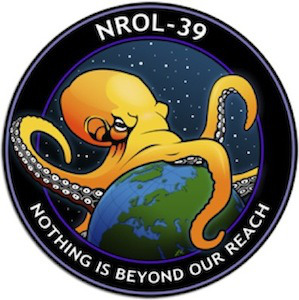
This is a really awesome article that explains the technical aspects in a way that makes sense to non-coders, without having to over simplify. I feel like this sort of writing should be much more appreciated. Also, the graphic at the top has no business being that good, this whole piece is a banger.
That’s so over the top bad it’s almost ridiculous
They might as well just publish the database credentials in the API too, jeez
They basically did. I bet they just used an ORM in the backed and then pointed the API endpoint to the user entity without filtering the fields. This results in a dump of the user table (although row by row indexed by users instead of a full dump)
Ahhhh, I was.wondering why they would take the time to set up an API with that data and forgot that almost everything has a way to just dump things into it without needing to be set. I forget because where I work we actively avoid that approach because of risks like this.
Oh dear, I had heard of this hack before, but I had not seen it laid out like this. Oh dear god, that’s bad.
Buy code on Fiverr, get code on Fiverr.